
Real Exam Questions and Answers as experienced in Test Center
500-443 Braindumps with 100% Guaranteed Actual Questions | https:alphernet.com.au
500-443 testing - Advanced Administration and Reporting of Contact Center Enterprise (CCEAAR) Updated: 2024 | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| killexams.com 500-443 Brain Dumps with Real Questions. Read and pass | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
 |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Exam Code: 500-443 Advanced Administration and Reporting of Contact Center Enterprise (CCEAAR) testing January 2024 by Killexams.com team | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Advanced Administration and Reporting of Contact Center Enterprise (CCEAAR) Cisco Administration testing | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Other Cisco exams010-151 Cisco Certified Technician (CCT) for Data Center500-275 Securing Cisco Networks with Sourcefire FireAMP Endpoints CICSP Cisco IronPort Certified Security Professional 600-455 Deploying Cisco Unified Contact Center Enterprise (DUCCE) 500-210 SP Optical Technology Field Engineer Representative 500-052 Deploying Cisco Unified Contact Center Express (UCCXD) 500-651 Security Architecture for Systems Engineer (SASE) 500-701 Cisco Video Infrastructure Design (VID) 500-301 Cisco Cloud Collaboration Solutions 500-551 Cisco Networking: On-Premise and Cloud Solutions 700-020 Cisco Video Sales Essentials 500-710 Cisco Video Infrastructure Implementation 700-105 Cisco Midsize Collaboration Solutions for Account Managers 500-325 Cisco Collaboration Servers and Appliances 500-490 Designing Cisco Enterprise Networks 500-470 Cisco Enterprise Networks SDA, SDWAN and ISE exam for System Engineers 500-901 Cisco Data Center Unified Computing Infrastructure Design 500-230 Cisco Service Provider Routing Field Engineer 700-150 Introduction to Cisco Sales 700-651 Cisco Collaboration Architecture Sales Essentials 700-751 Cisco SMB Product and Positioning Technical Overview (SMBSE) 300-410 Implementing Cisco Enterprise Advanced Routing and Services (ENARSI) 300-415 Implementing Cisco SD-WAN Solutions (ENSDWI) 300-420 Designing Cisco Enterprise Networks (ENSLD) 300-425 Designing Cisco Enterprise Wireless Networks (ENWLSD) 300-430 Implementing Cisco Enterprise Wireless Networks (ENWLSI) 2023 300-435 Automating Cisco Enterprise Solutions (ENAUTO) 300-510 Implementing Cisco Service Provider Advanced Routing Solutions (SPRI) 300-610 Designing Cisco Data Center Infrastructure (DCID) 300-615 Troubleshooting Cisco Data Center Infrastructure (DCIT) 300-620 Implementing Cisco Application Centric Infrastructure (DCACI) 300-635 Automating Cisco Data Center Solutions (DCAUTO) 300-810 Implementing Cisco Collaboration Applications (CLICA) 300-815 Implementing Cisco Advanced Call Control and Mobility Services (CLACCM) - CCNP 300-910 Implementing DevOps Solutions and Practices using Cisco Platforms (DEVOPS) 300-920 Developing Applications for Cisco Webex and Webex Devices (DEVWBX) 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) 350-501 Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR) 350-601 Implementing Cisco Data Center Core Technologies (DCCOR) 350-701 Implementing and Operating Cisco Security Core Technologies (SCOR) 350-801 Implementing Cisco Collaboration Core Technologies (CLCOR) 350-901 Developing Applications using Cisco Core Platforms and APIs (DEVCOR) 500-215 SP Mobility Technology Systems Engineer Representative 200-301 Cisco Certified Network Associate - CCNA 2023 100-490 Cisco Certified Technician Routing & Switching (RSTECH) 200-201 Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) 200-901 DevNet Associate (DEVASC) 300-535 Automating Cisco Service Provider Solutions (SPAUTO) 300-710 Securing Networks with Cisco Firepower 300-715 Implementing and Configuring Cisco Identity Services Engine 300-720 Securing Email with Cisco Email Security Appliance 300-725 Securing the Web with Cisco Web Security Appliance (SWSA) 300-730 Implementing Secure Solutions with Virtual Private Networks 300-735 Automating Cisco Security Solutions (SAUTO) 300-820 Implementing Cisco Collaboration Cloud and Edge Solutions 300-835 Automating Cisco Collaboration Solutions (CLAUTO) 500-440 Designing Cisco Unified Contact Center Enterprise (UCCED) 600-660 Implementing Cisco Application Centric Infrastructure - Advanced 300-515 Implementing Cisco Service Provider VPN Services (SPVI) 300-915 Developing Solutions Using Cisco IoT and Edge Platforms (DEVIOT) 300-215 Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR) 350-201 Performing CyberOps Using Core Security Technologies (CBRCOR) 500-240 Cisco Mobile Backhaul for Field Engineers (CMBFE) 700-765 Cisco Security Architecture for System Engineers 820-605 Cisco Customer Success Manager (CSM) 700-805 Cisco Renewals Manager (CRM) 500-452 Cisco Enterprise Networks Core and WAN (ENCWE) 700-760 Cisco Security Architecture for Account Managers 700-680 Cisco Collaboration SaaS Authorization (CSaaS) 700-846 Cisco IoT Advantage for Account Managers (IOTAAM)? 500-451 Cisco Enterprise Networks Unified Access exam (ENUAE) 500-920 Cisco Data Center Unified Computing Infrastructure Troubleshooting (DCITUC) 500-220 Cisco Meraki Solutions Specialist (ECMS) 500-560 Cisco Networking: On-Premise and Cloud Solutions 500-445 Cisco Contact Center Enterprise Chat and Email (CCECE) 500-442 Administering Cisco Contact Center Enterprise (CCEA) 500-265 Cisco Advanced Security Architecture System Engineer (ASASE) 700-755 Small Business Technical Overview (SBTO) 500-444 Cisco Contact Center Enterprise Implementation and Troubleshooting (CCEIT) 500-443 Advanced Administration and Reporting of Contact Center Enterprise (CCEAAR) | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| killexams.com offer valid and updated 500-443 VCE exam with genuine exam Q&A for new syllabus of 500-443 500-443 Exam. Practice their 500-443 Real Q&A to Excellerate your know-how and pass your exam with High Marks. They make sure your achievement in the Test Center, masking all of the Topics of exam and build your Knowledge of the 500-443 exam. Pass 4 sure with their correct questions. | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Question: 256 Which two call transfers are supported in PCCE Deployments? (Choose two.) A. SRTP Refer B. Release VXML Trunk Transfer C. CCE Managed Transfer D. CUCM Destination Transfer E. SIP Refer Answer: A,C,E Explanation: C CCE Managed Transfer is supported in PCCE Deployments, as it allows the agent to transfer a call to another agent or skill group within the same PCCE system using the Finesse desktop. E SIP Refer is supported in PCCE Deployments, as it allows the agent to transfer a call to an external destination using the SIP Refer method. Reference = [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 43; [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 101 Question: 257 What is the role of CVP in UCCE/PCCE? A. interface between CUBE and UCCE/PCCE B. queuing and self-service IVR C. call routing brain of PCCE/UCCE D. plays IVR Prompts to Callers Answer: B Explanation: The role of CVP in UCCE/PCCE is queuing and self-service IVR, as it provides voice response applications that can interact with callers, collect information, and queue calls for treatment by agents or other destinations. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 9 Question: 258 What is the role of a private network in UCCE/PCCE? $13$10 A. provides configuration updates from Logger to AW B. keeps each side of the duplex pair in sync C. replicates data from PG to Router D. communicates with the public network Answer: B Explanation: The private network in UCCE/PCCE provides a dedicated communication channel between the duplexed components, such as Logger, Router, and PG, and keeps each side of the duplex pair in sync. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 20 Question: 259 What is the maximum bytes (Data + Variable name) per payload in a PCCE deployment? A. 2000 B. 2400 C. 2500 D. 4800 Answer: C Explanation: The maximum bytes (Data + Variable name) per payload in a PCCE deployment is 2500 bytes. This is the limit imposed by the SIP protocol for the User to User Information (UUI) field that carries the ECC variables. Reference = [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 23 Question: 260 What are two ways to access UCCE/PCCE Servers? (Choose two.) A. ICA B. Web browser to access Web Administration tool C. RAW D. Secure Shell (SSHW1 E. Microsoft RDP Answer: A,B,D Explanation: A web browser can be used to access the Web Administration tool, which provides a graphical user interface for configuring and managing various aspects of the UCCE/PCCE system. D Secure Shell (SSH) can be used to access the UCCE/PCCE servers for command-line administration and troubleshooting. Reference = Administering Advanced Cisco Contact Center Enterprise (CCEAA), page 2; [Cisco Unified Contact Center Enterprise Installation and Upgrade $13$10 Guide, Release 12.5(1)], page 11 Question: 261 In PCCE 12k, what are two options to manage payloads? (Choose two.) A. a custom payload is created during the installation B. ECC Variables where Default Payload is the only option and all new ECC Variables are automatically added to the Custom Payload C. delete the default payload and rebuild with the same members D. ECC Variables where Custom payloads are added and new ECC Variables must be manually assigned to the appropriate payload E. a default payload is created during the installation Answer: A,D,E Explanation: ECC Variables where Custom payloads are added and new ECC Variables must be manually assigned to the appropriate payload is one of the options to manage payloads in PCCE 12k. E A default payload is created during the installation is another option to manage payloads in PCCE 12k. Reference = [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 24 Question: 262 Which protocol is used by UCCE/PCCE to communicate with CUCM? A. IH323 B. TAP1 C. JTAPI D. SIP Answer: C Explanation: The protocol used by UCCE/PCCE to communicate with CUCM is JTAPI, which stands for Java Telephony Application Programming Interface. JTAPI allows UCCE/PCCE to monitor and control agent phones and CTI ports on CUCM. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 10 Question: 263 What are two core components of PCCE? (Choose two.) A. CVP Call/VXML Server B. Agent PG A and B side $13$10 C. Cisco ECE Services Server D. CVP Reporting Server E. Cisco ECE Web server Answer: A,B Explanation: CVP Call/VXML Server is one of the core components of PCCE, as it provides voice response applications that can interact with callers, collect information, and queue calls for treatment by agents or other destinations. B Agent PG A and B side are another core components of PCCE, as they provide communication between CUCM and UCCE/PCCE components, such as Router, Logger, and CVP. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 9; Administering Advanced Cisco Contact Center Enterprise (CCEAA), page 3 Question: 264 Which protocol is used by CVP to communicate to VRU PG? A. GED-125 B. GED-155 C. GED-12.5 D. GED-256 Answer: B Explanation: The protocol used by CVP to communicate to VRU PG is GED-155, which stands for Generic External Device Protocol version 155. GED-155 allows CVP to send and receive messages from VRU PG for call control and data exchange. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 11 Question: 265 What are two XML files that will be backed up when the Disaster Recovery System performs a cluster-level backup? (Choose two.) A. drfSchedule.xml B. drfDevice.xml C. drfDeviceProfile.xml D. drfPlatform.xml E. drfSystem.xml Answer: A,E Explanation: $13$10 drfSchedule.xml is one of the XML files that will be backed up when the Disaster Recovery System performs a cluster-level backup, as it contains the information about the backup schedules. E drfSystem.xml is another XML file that will be backed up when the Disaster Recovery System performs a cluster-level backup, as it contains the information about the system components and their dependencies. Reference = [Cisco Unified Contact Center Enterprise Installation and Upgrade Guide, Release 12.5(1)], page 37 Question: 266 What are two mandatory ICM AW configurations to get the PCS working properly? (Choose two.) A. Configure the Survey DN, CT and associate with the Survey routing script. B. Set iser.microapp.isPostCallSurvev' to y after either the label node or the Queue to Skillgroup/PQ node in the initial incoming DN routing script logic. C. Set "user.microapp.isPostCallSurvey'' to n before either the label node or the Queue to Skillgroup/PQ node in the initial incoming DN routing script logic. D. Create a new call type for Post Call Survey, map incoming dialed number to a survey dialed number pattern, and associates the survey dialed number patterns to the survey call type. E. Create a new call type for Post Call Survey, map survey dialed number pattern to the incoming dialed number, and associate the incoming dialed number patterns to the survey call type. Answer: A,B Explanation: Configuring the Survey DN, CT and associate with the Survey routing script is one of the mandatory ICM AW configurations to get the PCS working properly, as it defines the destination and the treatment for the post call survey. B Setting user.microapp.isPostCallSurvey to y after either the label node or the Queue to Skillgroup/PQ node in the initial incoming DN routing script logic is another mandatory ICM AW configuration to get the PCS working properly, as it indicates that the call is eligible for post call survey. Reference = [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 25 Question: 267 What are two descriptions for JNDI? (Choose two.) A. a method for querying and updating data in a database B. designed to be independent of any specific directory service implementation so a variety of directories can be accessed C. a script that provides call routing! D. an API that defines how a client may access a database E. an API that provides naming and directory functionality to applications Answer: A,B,E Explanation: JNDI is designed to be independent of any specific directory service implementation so a variety of directories can be accessed, such as LDAP, NDS, or DNS. E JNDI is an API that provides naming and directory functionality to applications, such as looking up objects by name, binding objects to names, and creating and destroying naming $13$10 contexts. Reference = [Java Naming and Directory Interface (JNDI) Overview] Question: 268 What are two ways the Call Studio Application is built or executed? (Choose two.) A. VXML Server and Virtual Voice Browser execute the VXML application to provide service to the caller. B. Upload the Call Studio project to the Virtual Voice Browser (WB) server, where it resides as an application. C. The project is built using W D. The project is built using Call Studio. E. VXML Application can be called up via a CCE Routing Script using the Send to VRU Script node. Answer: A,D Explanation: VXML Server and Virtual Voice Browser execute the VXML application to provide service to the caller, such as playing prompts, collecting digits, or transferring calls. E VXML Application can be called up via a CCE Routing Script using the Send to VRU Script node, which sends a request to CVP for executing a specific VXML application. Reference = [Cisco Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 11; [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 16 Question: 269 ABC customer implemented Post Call Survey (PCS) for all Customer calls. However, the PCS flow did not engage for any of the calls. The CVP logs did not show any pieces of evidence that PCS requests had been made for the Caller. What is the first thing that should be Checked as part of troubleshooting in this scenario? A. Validate usermicroapp-isPostCallSurvey variable being set to y in the Main Routing Script. B. Check if the caller DN settings on SPOG has PCS enabled. C. Check if the Survey DN has a valid Call type and is associated with the routing script to play desired prompts. D. Check if the caller DN settings on SPOG has valid PCS DN patterns configured. Answer: D Explanation: The first thing that should be Checked as part of troubleshooting in this scenario is D. Check if the caller DN settings on SPOG has valid PCS DN patterns configured. According to the Cisco Packaged Contact Center Enterprise Features Guide, Release 12.0 (1), the mapping of a dialed number pattern to a Post Call Survey number enables the Post Call Survey feature for the call1. Therefore, if the caller DN settings on SPOG do not have valid PCS DN patterns configured, the Post Call Survey feature will not be triggered for any of the calls. The other options are not the first thing to verify, because they are either related to the Post Call Survey script or the expanded call variable that controls Post Call Survey, which are not relevant if the PCS DN patterns are not configured correctly. $13$10 Question: 270 Which Routing Script logic helps to invoke the Post Call Survey successfully? A. If the script completes after going to an Agent, the call is directed to the Post Call Survey dialed number. B. To offer the PCS for all incoming DNs. there is no need to explicitly set the variable in the Main script. It is set to n by default. C. If the script completes without going to an Agent, the call is directed to the Post Call Survey dialed number. D. To offer the PCS for specific incoming DN's. the variable needs to be set in the Main script explicitly as n. Answer: A Explanation: According to the Cisco Packaged Contact Center Enterprise Features Guide, Release 12.0 (1), a Post Call Survey is triggered by the hang-up event from the last agent1. When the agent hangs up, the call routing script launches a survey script. The value of the expanded call variable user.microapp.isPostCallSurvey controls whether the call is transferred to the Post Call Survey number. If user.microapp.isPostCallSurvey is set to y (the implied default), the call is transferred to the mapped post call survey number. If user.microapp.isPostCallSurvey is set to n, the call ends1. Therefore, to invoke the Post Call Survey successfully, the routing script logic should direct the call to the Post Call Survey dialed number after the agent disconnects from the caller. The other options are not correct, because they either do not involve an agent interaction or do not set the user.microapp.isPostCallSurvey variable correctly. Reference: 1: Cisco Packaged Contact Center Enterprise Features Guide, Release 12.0 (1) - Post Call Survey Question: 271 When an explicit or implicit Send to VRU node is encountered, a default Label is returned to CVR This Label, along with a unique correlation ID, is delivered to CVR The CVP delivers this string via SIP invite to the Virtual Voice Browser (WB). At this point, which two actions does the WB take? (Choose two.) A. The WB will check if a media server is set up or not. B. The WB will drop the call. C. The WB will ask the ICM script for instruction. D. The comprehensive WB script will initiate an RTP session between the Ingress Gateway and an allocated WB E. It invokes a comprehensive application in the Virtual Voice Browser. Answer: A,C,D Explanation: When an explicit or implicit Send to VRU node is encountered, a default Label is returned to CVP. This Label, along with a unique correlation ID, is delivered to CVP. The CVP delivers this string via SIP invite to the Virtual Voice Browser (VVB). At this point, the VVB will ask the ICM script for instruction, such as which VXML application to execute. D When an explicit or implicit Send to VRU node is encountered, a default Label is returned to CVP. This Label, along with a unique correlation ID, is delivered to CVP. The CVP delivers this string via SIP invite to the Virtual Voice Browser (VVB). At this point, the comprehensive VVB script will initiate an RTP session between the Ingress Gateway and an allocated VVB, which will play prompts and collect digits from the caller. Reference = [Cisco $13$10 Unified Contact Center Enterprise Solution Reference Network Design (SRND), Release 12.5(1)], page 11; [Cisco Unified Contact Center Enterprise Features Guide, Release 12.5(1)], page 16 Question: 273 Where must a Dialed Number be mapped within CCE? A. Call Type, which in turn points to a scheduled Routing Script B. Precision queue C. Skill group D. Media Server Answer: A Explanation: A Dialed Number must be mapped within CCE to a Call Type, which in turn points to a scheduled Routing Script. This allows CCE to route calls based on the dialed number and apply different treatments and reports for different call types. Reference = Advanced Administration and Reporting of Contact Center Enterprise (CCEAAR), page 2 $13$10 | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||

Getty Images
Roughly 11 million Internet-exposed servers remain susceptible to a recently discovered vulnerability that allows attackers with a foothold inside affected networks. Once they're in, attackers compromise the integrity of SSH sessions that form the lynchpin for admins to securely connect to computers inside the cloud and other sensitive environments. Terrapin, as the vulnerability has been named, came to light two weeks ago in a research paper published by academic researchers. Tracked as CVE-2023-48795, the attack the researchers devised works when attackers have an adversary-in-the-middle attack (also abbreviated as AitM and known as man-in-the-middle or MitM), such as when they’re positioned on the same local network and can secretly intercept communications and assume the identity of both the recipient and the sender.In those instances, Terrapin allows attackers to alter or corrupt information transmitted in the SSH data stream during the handshake—the earliest connection stage, when the two parties negotiate the encryption parameters they will use to establish a secure connection. As such, Terrapin represents the first practical cryptographic attack targeting the integrity of the SSH protocol itself. It works by targeting BPP (Binary Packet Protocol), which is designed to ensure AitMs can’t add or drop messages exchanged during the handshake. This prefix truncation attack works when implementations support either the "ChaCha20-Poly1305" or "CBC with Encrypt-then-MAC," cipher modes, which, at the time the paper was published, was found in 77 percent of SSH servers. Internet-wide scans performed Tuesday, the last day such data was available at the time of reporting, revealed that more than 11 million IP addresses exposing an SSH server remained vulnerable to Terrapin. Nearly a third of those addresses, 3.3 million, resided in the US, followed by China, Russia, Germany, Russia and Singapore. All of the unpatched implementations tracked by Shadowserver supported the required cipher modes. 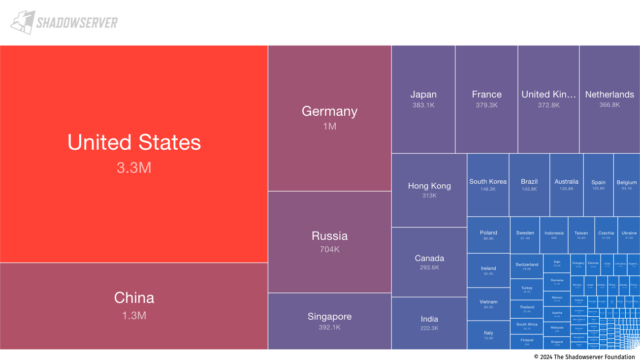
Enlarge / Tree map for CVE-2023-48795.
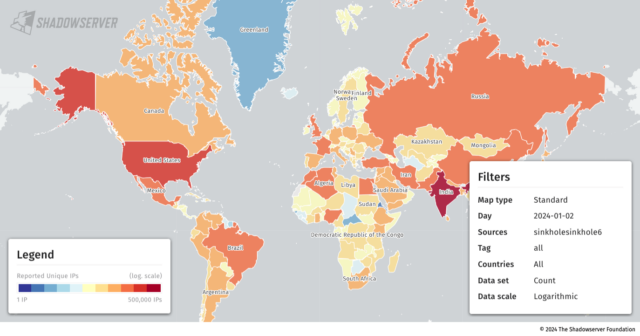
Enlarge / World map of countries unpatched against CVE-2023-48795.
Shadowserver
Only 53 of the vulnerable instances relied on implementations of AsyncSSH, the only app currently known to be seriously affected by Terrapin. Two vulnerabilities the researchers discovered in AsyncSSH allowed Terrapin to (1) downgrade security extensions that organizations to replace the extension information message sent by the server, letting the attacker control its content or (2) control the remote end of an SSH client session by either injecting or removing packets or emulating the shell established. AsyncSSH has patched those two vulnerabilities, tracked as CVE-2023-46445 and CVE-2023-46446, in addition to CVE-2023-48795, the Terrapin vulnerability affecting the SSH protocol. It appears the overwhelming majority of AsyncSSH users have installed the patches. The requirement of an AitM position and the lack of currently known practical attacks made possible by Terrapin are important mitigating factors that some critics say have been lost in some news coverage. That said, at this stage, there are few good reasons not to have patched the protocol flaw by now, since patches became widely available about one to two weeks ago. “The attack requires quite a bit of complexity in that MitM is necessary, so that will limit practical application to more targeted attacks in their view,” Piotr Kijewski, a Shadowserer researcher, wrote in an email to Ars. “So unlikely to have this mass-exploited. Still, the sheer mass of vulnerable instances suggests this vulnerability will be with us for years to come and that in itself makes it attractive in some specific cases.” Optional caption
While it’s unlikely that Terrapin will ever be mass-exploited, the potential remains for it to be used in targeted attacks by more sophisticated attackers, such as those backed by nation-states. Despite earlier versions of AsyncSSH being the only known application vulnerable to practical Terrapin attacks, the researchers spent little time analyzing other implementations. Adversaries with more time, resources, and motivation could identify other vulnerable implementations. Kijewski listed the top 50 banners displayed by vulnerable IP addresses as:
Patching Terrapin isn’t straightforward, because of the sheer number of implementations affected and the necessity that apps running on both the admin client and the server be patched. The researchers listed the following implementations as vulnerable and included links to patches when available. Asterisks indicate application developers contacted prior to the release of the research paper:
It is the responsibility of faculty to make their tests accessible. That said, there are many times when faculty are unable to provide a necessary test accommodation. In these cases, students may schedule exams with Disability Resources through their Test Accessibility Services (TAS). These are the steps students should take if they wish to use their test accommodations. Please note that Disability Resources only administers exams for students who have affiliated with their office.
Jeremy Zhe-Heimerman, Assistant Director, Disability Resources Memorial Library, B-121A It is the responsibility of faculty to provide accessible tests at SUNY Cortland. That said, there are many times when instructors are unable to provide a necessary test accommodation. In these cases, Disability Resources will do so as a service to faculty through Test Accessibility Services (TAS). Please note that TAS is only available to students who have registered with Disability Resources. These are the steps an instructor should take if a student comes to you with an accommodations letter.
Contact: tas@cortland.edu Jeremy Zhe-Heimerman, Assistant Director, Disability Resources Memorial Library, B-121A Since 1969, we've been selecting the right applicants for Bowdoin, using only the materials that they require of you: your transcripts, your writing, and how your teachers talk about you. This policy allows applicants to decide for themselves whether or not their SAT or ACT results accurately reflect their academic ability and potential. For candidates electing to submit them, test scores will be reviewed along with other indicators of academic ability. Forty-six percent of students in the Class of 2026 chose not to submit their scores. Score SuppressionApplicants indicate on their applications whether they would like Bowdoin to review their standardized test results. Applicants also have the option to select some test types and not others for review (for example, a student might choose to use their SAT scores, but not their ACT). Applicants have until the application deadline to suppress their scores.
Bowdoin will not review selected sections of an SAT or an ACT score (for example, just the Science portion of the ACT). If an applicant chooses to include scores for a specific test type, Bowdoin will review the complete score for that test type. SuperscoringBowdoin will "superscore" the SAT. Meaning, the admissions committee will consider the highest Critical Reading, Math, and Writing Scores submitted by an applicant, irrespective of test date. Bowdoin will NOT combine results from Redesigned and pre-Redesign SAT exams to create a new total score. They will superscore Redesigned and pre-Redesign results separately, considering the highest section and total scores submitted from either set of results. Bowdoin also superscores the ACT. The admissions committee will consider the highest submitted Composite score and subsection scores, and will also recalculate a new Composite score from subsection scores earned on different test dates. Score ReportsFor students submitting standardized test scores, they will accept scores that are self-reported on the student’s application, reported by the testing agency, or submitted through the self-report form found in the Bowdoin Application Portal. They accept self-reported scores for all applicants. Bowdoin will verify scores for all enrolling students. Discrepancies between self-reported and official scores may jeopardize a student’s place at Bowdoin. Official Score ReportsWe will accept scores reported on a school transcript or sent to their office by a school counselor or CBO advisor as official. Official score reports may be sent to their office by email, fax, mail, or directly from the testing agency. Our testing codes are: 3089 (College Board) and 1636 (ACT). Is standardized testing required for certain applicants?No. Bowdoin College is test-optional for all applicants. Homeschooled candidates can find further information on additional requirements and recommendations on the Homeschooled Students page. International applicants can find more information about required English proficiency testing on the International Applicant page. This story first appeared at ProPublica. ProPublica is a Pulitzer Prize-winning investigative newsroom. Sign up for The Big Story newsletter to receive stories like this one in your inbox. Since May, the Trump administration has paid a fledgling Texas company $7.3 million for test tubes needed in tracking the spread of the coronavirus nationwide. But, instead of the standard vials, Fillakit LLC has supplied plastic tubes made for bottling soda, which state health officials say are unusable. The state officials say that these “preforms,” which are designed to be expanded with heat and pressure into 2-liter soda bottles, don’t fit the racks used in laboratory analysis of test samples. Even if the bottles were the right size, experts say, the company’s process likely contaminated the tubes and could yield false test results. Fillakit employees, some not wearing masks, gathered the miniature soda bottles with snow shovels and dumped them into plastic bins before squirting saline into them, all in the open air, according to former employees and ProPublica’s observation of the company’s operations. “It wasn’t even clean, let alone sterile,” said Teresa Green, a retired science teacher who worked at Fillakit’s makeshift warehouse outside of Houston for two weeks before leaving out of frustration. The Federal Emergency Management Agency signed its first deal with Fillakit on May 7, just six days after the company was formed by an ex-telemarketer repeatedly accused of fraudulent practices over the past two decades. Fillakit has supplied a total of more than 3 million tubes, which FEMA then approved and sent to all 50 states. If the company fulfills its contractual obligation to provide 4 million tubes, it will receive a total of $10.16 million. Officials in New York, New Jersey, Texas and New Mexico confirmed they can’t use the Fillakit tubes. Three other states told ProPublica that they received Fillakit supplies and have not distributed them to testing sites. FEMA has asked health officials in several states to find an alternative use for the unfinished soda bottles. “We are still trying to identify an alternative use,” said Janelle Fleming, a spokeswoman for the New Jersey Department of Health. Fillakit owner Paul Wexler acknowledged that the tubes are normally used for soda bottles but otherwise declined to comment. The Fillakit deal shows the perils of the Trump administration’s frantic hiring of first-time federal contractors with little scrutiny during the pandemic. The federal government has awarded more than $2 billion to first-time contractors for work related to the coronavirus, a ProPublica analysis of purchasing data shows. Many of those companies, like Fillakit, had no experience with medical supplies. The U.S. has lagged behind many European countries in its rate of testing people for the coronavirus, partly because of supply shortages or inadequacies. Epidemiologists say testing is vital to tracking the virus and slowing transmission. In at least one state, the shipment of unusable Fillakit tubes contributed to delays in rolling out widespread testing. “They’re the most unusable tubes I’ve ever seen,” said a top public health scientist in that state, who asked to remain anonymous to protect his job. “They’re going to sit in a warehouse and no one can use them. They won’t be able to do their full plan.” In a written response to questions, FEMA said it inspects testing products “to ensure packaging is intact to maintain sterility; that the packing slip matches the requested product ordered, and that the vials are not leaking.” It said that “product validation” that medical supplies are effective “is reinforced at the state laboratories.” The agency did not answer questions about the size and lack of sterilization of Fillakit’s tubes or about why it sought an alternative use for them. Fillakit is one of more than 300 new federal contractors providing supplies related to COVID-19. A ProPublica analysis last month found about 13% of total federal government spending on pandemic-related contracts went to first-time vendors. FEMA said last month that it only pays for products once they have been delivered, minimizing the risk of wasting taxpayer dollars. “FEMA does not enter into contracts unless it has reason to believe they will be successfully executed,” it said. Preforms, the small tubes also known in the plastics industry as “baby soda bottles” or “blanks,” have a following among elementary school science teachers and amateur scientists, but they don’t meet rigorous laboratory standards. They’re much cheaper than glass vials and can be sealed off with a soda bottle cap. When inflated with high-pressure air, the soft plastic expands to the size of a 2-liter soda bottle. The preforms arrive at Fillakit’s warehouse in a huge shipping container. The tubes are then shoveled into smaller bins. Workers add the saline solution and screw on caps. The tubes are then loosely piled in bags and sent to FEMA, which forwards them to the states. Typically, test tubes are individually packaged to guard against contamination. Washington state, an epicenter of the first outbreak of the virus, got more than 76,000 Fillakit vials from FEMA. None can be used. “They were packaged unusually,” said Frank Ameduri, a spokesman for the state Health Department. “Not in a way we’re used to seeing, and they were not labeled. Some of them have been sent to their lab for quality control. None of the vials will be used until we’ve identified what’s in them and that they are safe for use.” About 140,000 Fillakit tubes are also shelved in Texas, where officials were slow to roll out testing. The number of confirmed cases in Texas has increased by more than one-third in the past two weeks, according to data gathered by The COVID Tracking Project. “There were issues with the labeling, and they use saline rather than viral transport medium, so they have not used them for their testing efforts,” said Chris Van Deusen, a spokesman for the Texas health department. The U.S. Food and Drug Administration has only validated one solution, known as viral transport medium, as reliable in preserving the coronavirus RNA from decay or destruction by substances in the container. However, because that medium is in short supply, the FDA has also granted an emergency authorization for other products it believes can keep the virus intact for up to three days. Fillakit has been squirting one of the alternatives into its tubes, phosphate buffered saline, which the FDA says should be placed into “a sterile glass or plastic vial.” A spokeswoman for the Maryland-based Association of Public Health Laboratories, a membership organization that writes best practices and helps connect public health labs with government agencies, said it has heard rumblings about Fillakit’s tubes but “nothing deadly.” “The bigger issue is the size of the tubes,” said the spokeswoman, Michelle Forman. “They are an unusual shape so they don’t fit racks, and they are getting lots of pushback about how difficult it is to work with them from their clinical partners.” Richard Loeb, a contract law expert at the University of Baltimore, said FEMA has the power to claw back money paid to contractors, remove them from the government’s list of approved vendors or refer them to the agency’s inspector general. “It’s outrageous enough that they [FEMA] ordered something to test for COVID-19, and they got something that can’t be used to test for COVID-19,” Loeb said. “I still am a little bit troubled as to why FEMA accepted them. … They may have stupidly accepted something that was nonconforming.” Wexler, Fillakit’s owner, has a background in law and real estate, not medical supplies. In 2012, the Federal Trade Commission accused Wexler and his telemarketing firm of illegal robocalling, making unauthorized charges to consumers’ bank accounts and falsely claiming to be a nonprofit organization. Wexler’s firm allegedly misrepresented itself as a credit counseling service for several years, charging customers for work it did not do, according to court records. Wexler, who denied the charges, settled the case a year later. The settlement banned him from offering debt relief services — but not from being a federal contractor — and imposed a $2.7 million judgment. Fillakit and another Wexler company, Cleargate Labs, operate out of the same warehouse in The Woodlands, a sprawling Houston suburb. Cleargate describes itself as a “network of primary clinical laboratories” on its website. Last year, the company cold-called an elderly Iowa woman, told her that it was marketing a DNA screening for cancer genes and offered to send her testing supplies in exchange for her Medicare number, the Tampa Bay Times reported. Suspecting a scam, the woman reported the company to local law enforcement. Cleargate did not bill her and was not charged with a crime. Three former Fillakit employees said that its process was unsterile. Workers shoveled up the tubes from unsanitary surfaces. The liquid that they added to each tube to preserve samples for lab analysis was kept in trays exposed to the air, which was whipped around by large fans. Standards were compromised in the rush to meet productivity goals, Green said. “At the beginning, they were being picky, saying, ‘You have to make sure it’s at least 2 milliliters.’ And sometimes there were tubes that didn’t have any [solution] in there,” she said. Wexler would come in and “cuss and scream at everybody in this warehouse about how nobody’s paying attention to what they’re doing,” she said. Wexler and Stephen Wachtler, a manager at Cleargate and Fillakit, “were telling us, ‘Yeah, they gotta have four bins by lunch,’” Green said. “‘We gotta have 10 bins before you leave at 5 o’clock. Work faster, work faster.’” Green said that few employees at the company had backgrounds in science or medicine. In May, during Fillakit’s first week of operations, the company did not provide workers with face masks, she said, raising concerns that fluid from their noses and mouths could land inside the tubes. Later, supervisors did hand out masks but did not require employees to wear them. On June 10, a ProPublica reporter observed workers, some not wearing masks, standing over snow shovels and bins of tiny soda bottles. Wexler and workers loaded a shipment of tubes into an Enterprise rental truck, which lacked the refrigeration that the Centers for Disease Control and Prevention say is needed to safely transport legitimate testing supplies. Wexler denied a request to tour the warehouse. Asked about the lack of sterile conditions and the use of soda preforms, Wexler screamed, “What’s your problem, man?” Michelle Hardy, a retired nurse who worked at Fillakit through June 10, said her concerns about contamination were dismissed by Wachtler. He did not respond to requests for comment. “I kind of said to Stephen, ‘Is this supposed to be, like, clean technique, or sterile technique or what?’” Hardy said. “He’s like: ‘No, it’s fine. It’s fine what you’re doing because they’re just testing for COVID, and so if there’s any other bacteria or viruses in there then it’s not going to show up.’” That’s not true, according to Vjollca Konjufca, an associate professor of microbiology at Southern Illinois University. If Fillakit employees were infected, they might have contaminated the tubes with their own virus, potentially causing false test results, she said. Konjufca was part of a team at her university that manufactured the viral transport solution validated by the FDA. She said they followed strict protocols to ensure tests aren’t contaminated. “We filter-sterilize, and then they add antibiotics,” Konjufca said. “The whole work is handled under a biosafety hood … so it does not allow any sort of air from the room, particulates or whatever, to get into your vials.” There are many ways to mess up medical testing, so careful manufacturing is vital. Some substances in saliva or the plastic vials can damage virus RNA and alter test results, Konjufca said. “You cannot just makeshift use soda bottles to make tubes,” she said. “You have enzymes in there and you have contaminants that can mess up the results.”
Terranet has been awarded a grant of 614 000 SEK from the Swedish Transport Administration's Skyltfonden for a joint project with RISE’s test bed AstaZero. The project, which runs throughout all of 2024, aims to Excellerate traffic safety for unprotected road users by developing new testing methods and technologies for advanced driver assistance systems (ADAS). Titled "Significant Accident and Injury Reduction for Unprotected Road Users with New ADAS Methods and Technologies," the project seeks to develop new testing and verification methods for BlincVision and state-of-the-art ADAS systems for autonomous emergency braking (AEB) in time-critical accident scenarios. The project includes six work packages to be carried out over the year 2024:
"The project is an important step forward towards their goal of making urban traffic safer. With funding from the Swedish Transport Administration, AstaZero's expertise, and their own technical competence, they are confident that they can advance both their product development and the industry's testing methods," says Magnus Andersson, CEO of Terranet. About Skyltfonden For more information, please contact About Terranet AB (publ) Terranet is on a mission to save lives in urban traffic. We develop breakthrough tech solutions for Advanced Driver Assistance Systems (ADAS) and Autonomous Vehicles (AV) that protect vulnerable road users. With a unique and patented vision technology, Terranet’s anti-collision system BlincVision scans and detects road objects multiple times faster and with higher accuracy than any other ADAS technology available today. Terranet is based in Lund, Sweden, and in the heart of the European automotive industry in Stuttgart, Germany. The company is listed on Nasdaq First North Premier Growth Market since 2017(Nasdaq: TERRNT-B). Follow their journey at www.terranet.se Certified Adviser to Terranet is Mangold Fondkommission AB, 08-503 015 50, ca@mangold.se. Attachment | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
500-443 information source | 500-443 information source | 500-443 outline | 500-443 Practice Test | 500-443 certification | 500-443 learn | 500-443 answers | 500-443 exam success | 500-443 guide | 500-443 reality | | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Killexams exam Simulator Killexams Questions and Answers Killexams Exams List Search Exams |
500-443 Reviews by Customers
Customer Reviews help to evaluate the exam performance in real test. Here all the reviews, reputation, success stories and ripoff reports provided.
100% Valid and Up to Date 500-443 Exam Questions
We hereby announce with the collaboration of world's leader in Certification Exam Dumps and Real Exam Questions with Practice Tests that, we offer Real Exam Questions of thousands of Certification Exams Free PDF with up to date VCE exam simulator Software.







